Today, I updated the “transposition analyzer” component of CrypTool 2 (CT2) to make its usage more convenient. The analyzer allows the cryptanalysis of ciphertexts that are encrypted using the columnar transposition cipher. It was written some time ago in the early days of CT2 by some of my commolitons when I was doing my masters.
It always bugged me that you needed to restart the analyzer when you wanted to analyze different key lengths. For example, if you assumed that a ciphertext had been encrypted using a columnar transposition cipher, but you were unsure which key length had been used (e.g. between 5 and 15), you had to restart it for any of the assumed key lengths.
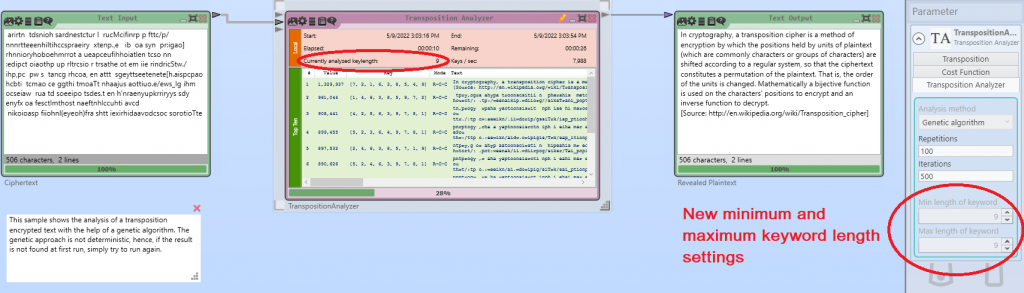
Now, its a matter of setting minimum and maximum key lengths, and the analyzer will test all lengths of the defined range 🙂
Btw, the transposition analyzer supports different cryptanalysis methods/heuristics: brute-force for smaller key lengths, genetic algorithm and hillclimbing for longer key lengths. Also, if you have a crib (a part of known plaintext), the crib analysis can be used.
But besides simply just updating the component, I fixed a few bugs and generally improved the C# code a bit 🙂
If you want to see how to use the transposition analyzer of CT2, I created a video about it in the past:
Probably, I will also create a new video about columnar transposition ciphers and the updated transposition analyzer in the near future.
We published some years ago a paper about cryptanalysis of the columnar transposition cipher in Cryptologia [1].
Finally, if you want to simply encrypt or decrypt using the columnar transposition cipher, you may have a look at the nice implementation in CrypToolOnline: https://www.cryptool.org/en/cto/transposition
[1] Lasry, George, Nils Kopal, and Arno Wacker. “Cryptanalysis of columnar transposition cipher with long keys.” Cryptologia 40.4 (2016): 374-398.
Nils
